Comprehensive Rules
Rewrite reality. 50+ actions, mock responses, spoof DNS, throttle bandwidth, fake auth. Edit visually or dive into YAML.
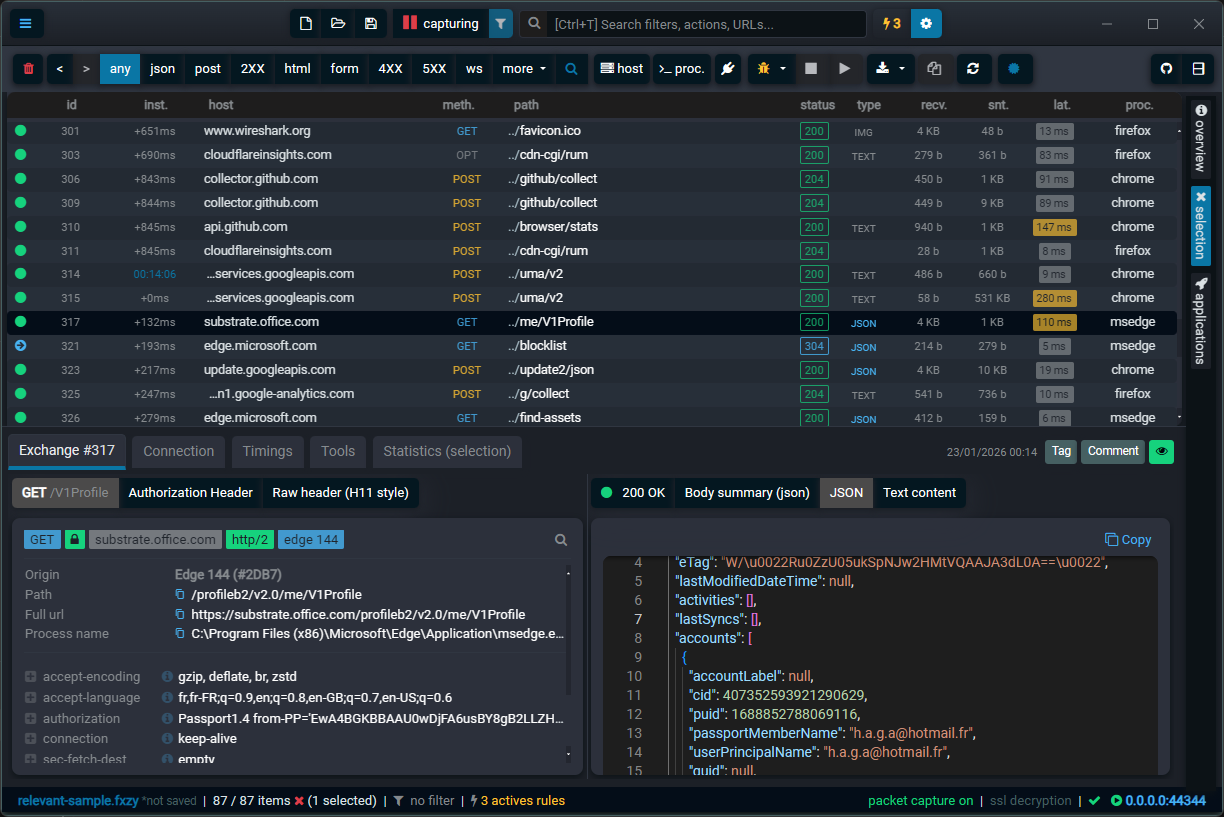
Wire-level capture for every modern protocol. REST, OAuth, gRPC, LLM streams, fully decoded and ready for breakpoints, mocking, and replay.
Rewrite reality. 50+ actions, mock responses, spoof DNS, throttle bandwidth, fake auth. Edit visually or dive into YAML.
Skip the system proxy dance. Launch Chrome, Firefox, or any app directly, already hooked and ready to intercept. Zero config.
Pause traffic at any stage, DNS lookup, before request, after headers. Step through the network like stepping through code.
One click, and Fluxzy becomes your system proxy. Every HTTP request from every app flows through, no manual browser config needed.
PCAP recording is live. Every packet gets saved, not just HTTP, the whole conversation. Wireshark-ready, no extra tools.
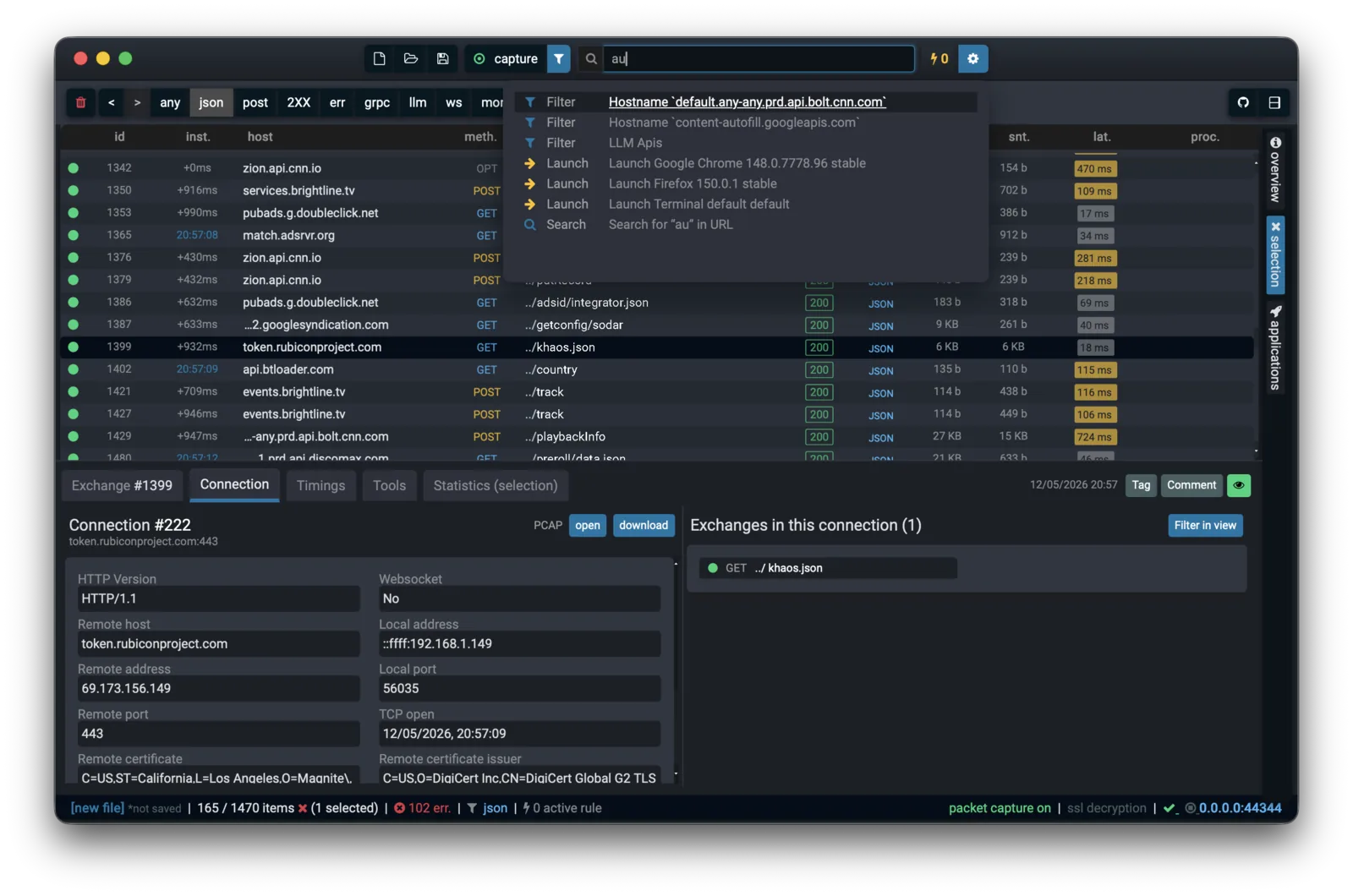
Ctrl+T your way through Fluxzy. Jump to filters, rules, settings, exchanges, anything. Type what you need and you're there.
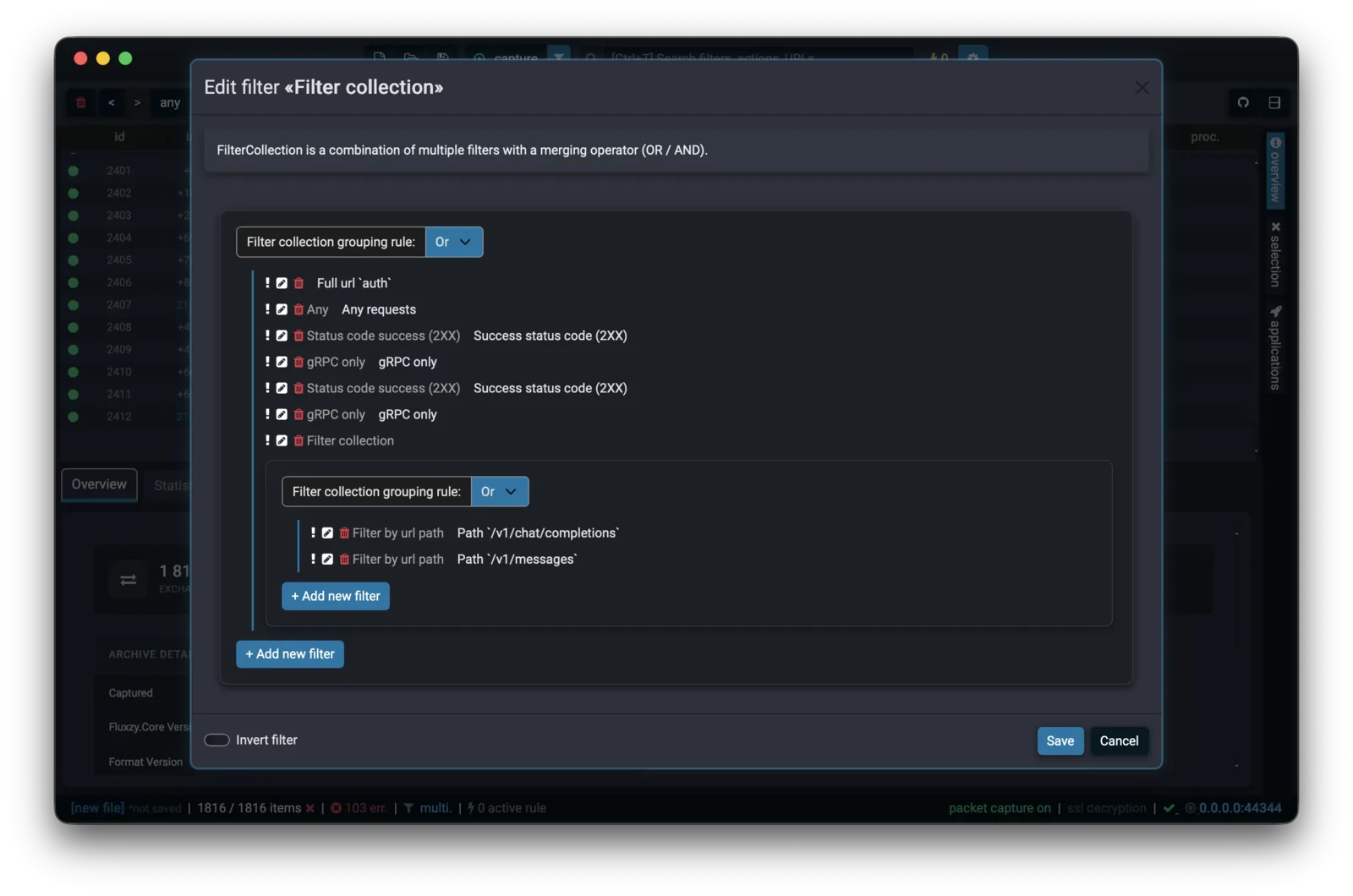
Find anything, fast. Ctrl+click to stack filters with AND, Shift+click for OR. Ctrl+Shift live debugs the next matching request. Create and save filter.
Full Monaco editor for your response body. Syntax highlighting, code folding, search, the same editor powering VS Code.
Select two exchanges, hit diff. Headers, body, cookies—everything side by side, changes highlighted. Find what broke between "it worked yesterday" and "it's broken now" in seconds.
Six reasons developers switch from Fiddler and Charles
The interception engine behind Fluxzy is fully open source. Every cryptographic decision, every stream transformation: auditable and extensible. No black box proxying your traffic.
github.com/haga-rak/fluxzy.coreNo account required. No cloud sync. No "sign in to continue." Fluxzy is good old-fashioned desktop software that works without an internet connection. Your traffic data stays on your machine, period.
Download FluxzyNative performance, fraction of the memory footprint. Opens large archive files without choking. Fluxzy won't eat your RAM for breakfast.
Explore featuresInspect and modify gRPC calls with the same workflow you use for REST. Bring your own proto files for decoded, human-readable views.
gRPC debugging guideTwo TLS engines (system default or BouncyCastle). Raw PCAPNG capture with embedded SSL keys. HTTP/1.1, HTTP/2, WebSocket, SOCKS5, all first-class.
See all protocolsBreakpoints, live editing, response mocking, request replay, DNS spoofing, bandwidth throttling, 75k+ req/s throughput. Plus a YAML-based rule engine with 100+ built-in filters and actions for codeless traffic alteration.
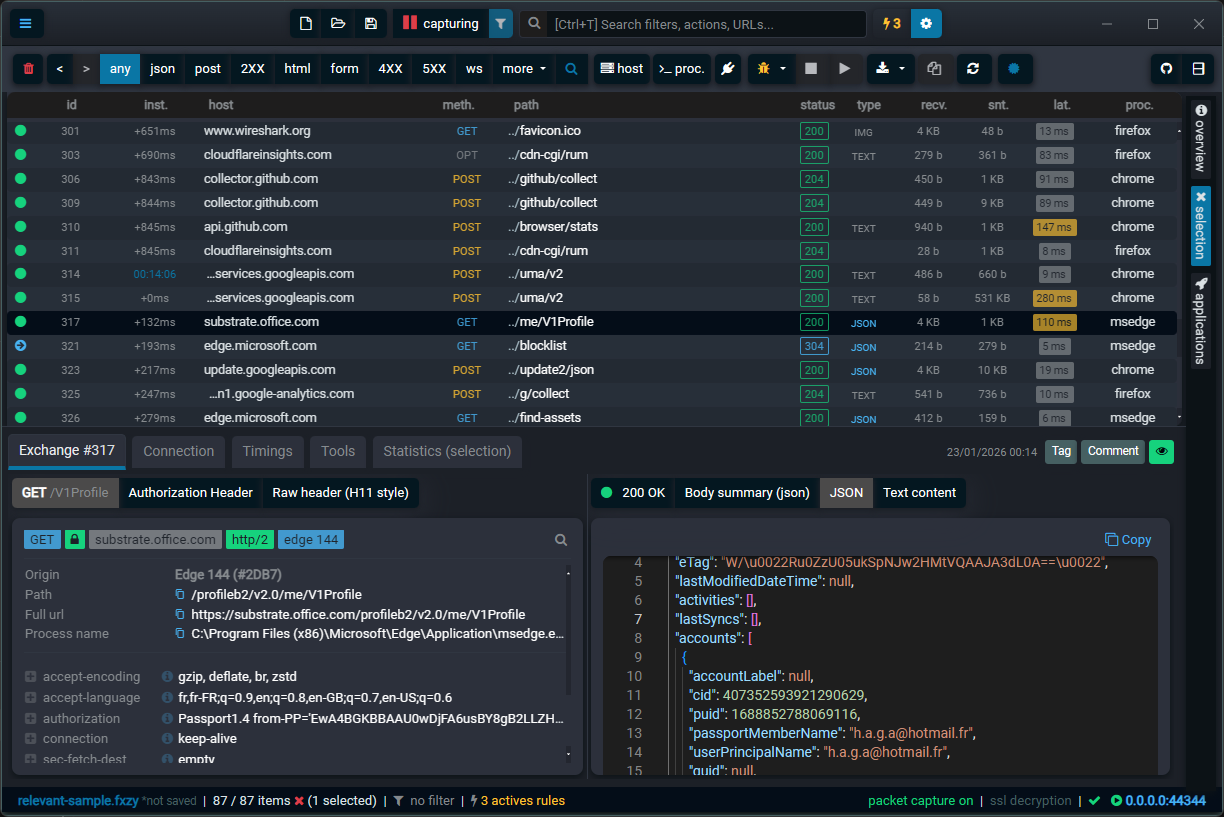
Breakpoints & live editJWTs decoded, LLM streams parsed, gRPC frames structured, rules nested as deep as you need.
Fluxzy reads what flows over the wire. JWTs are split into header, payload and signature with algorithm and expiry exposed. LLM API calls (OpenAI, Anthropic, Gemini) are decoded into model, tool calls, tool choices, token usage and prompts. gRPC frames are unwrapped into typed messages. Response bodies open in a Monaco editor (the same engine that powers VS Code), with syntax highlighting, code folding and search.
Intercept gRPC sessions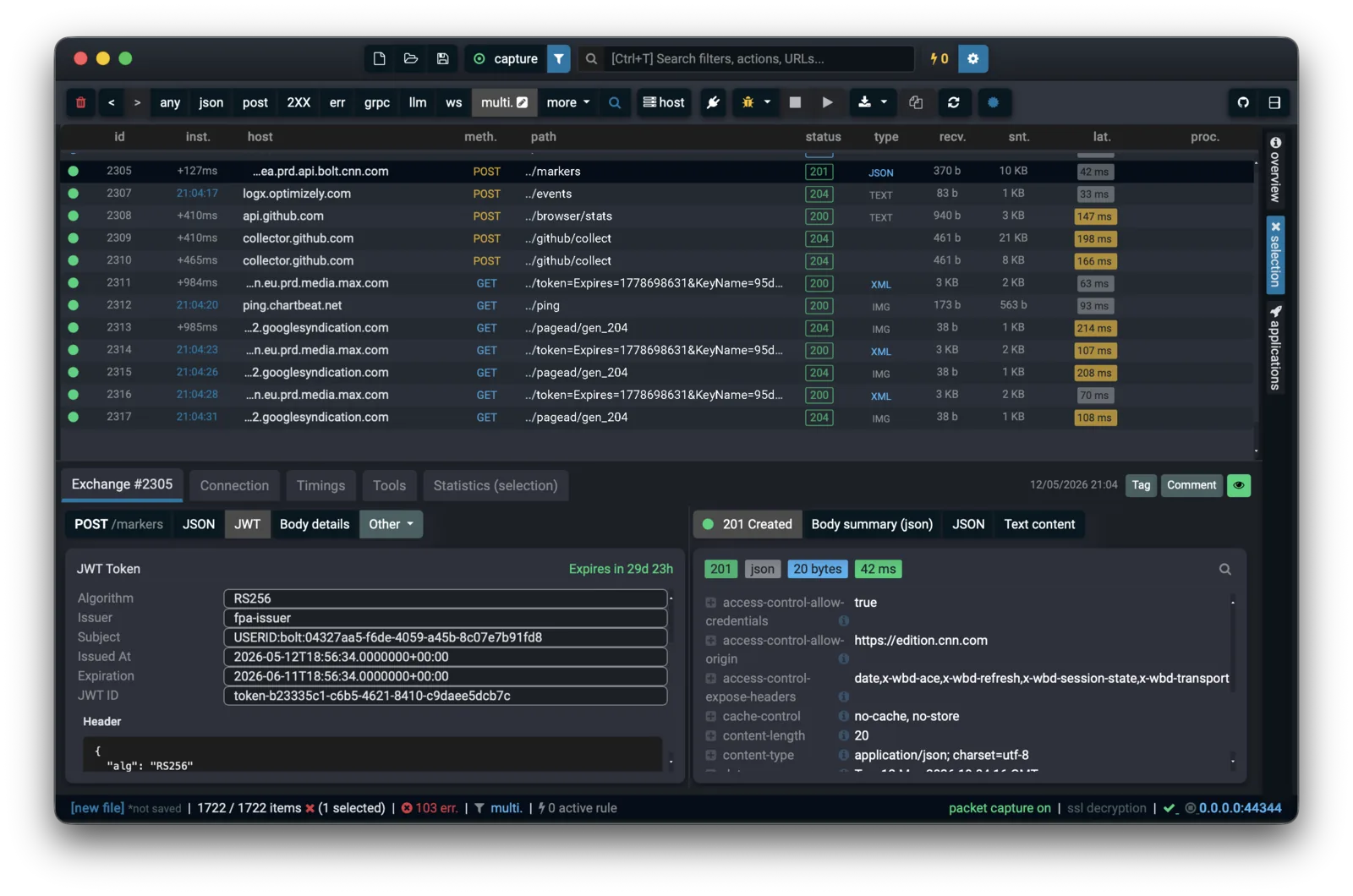
Every part of an exchange can be transformed: request line, headers, body, TLS fingerprint, DNS resolution, upstream proxy, bandwidth. 50+ built-in actions and 50+ filters combine with nested AND/OR groups, so a single rule can target POST /v1/chat/completions on api.openai.com while excluding gRPC traffic.
Skip the system-proxy dance. Fluxzy detects installed browsers (Chrome, Firefox, Brave, Edge) and shells (PowerShell, cmd, macOS Terminal, GNOME Terminal, Ptyxis) and launches them already routed through the capture session. For everything else, generate a bootstrap script that exports the right environment variables for Node, Python, Ruby, Go, Rust, .NET, package managers and Git.
Intercept browser traffic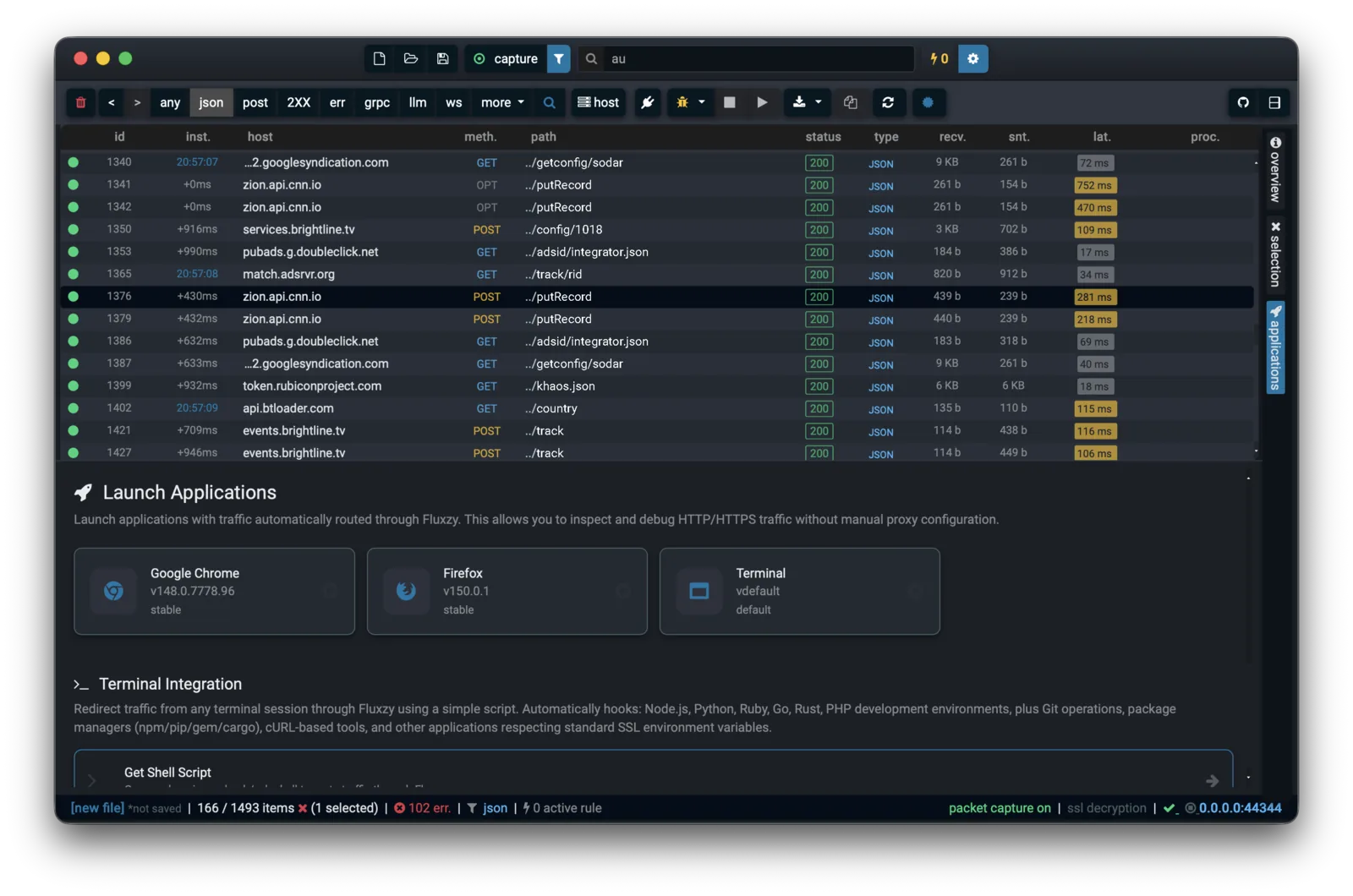
One palette across the whole app. Type a host, an action, a filter, an exchange ID or a setting, and Fluxzy ranks every match and jumps you there. The same shortcut that fuzzy-finds an action opens global DNS-over-HTTPS settings or filters the grid to 5xx in two keystrokes.
Pause traffic at DNS lookup, before request, after headers or on response. Edit URL, method, headers and body in place. Resume one step at a time, or all at once. The same workflow as stepping through code, applied to the network.
Breakpoints & live edit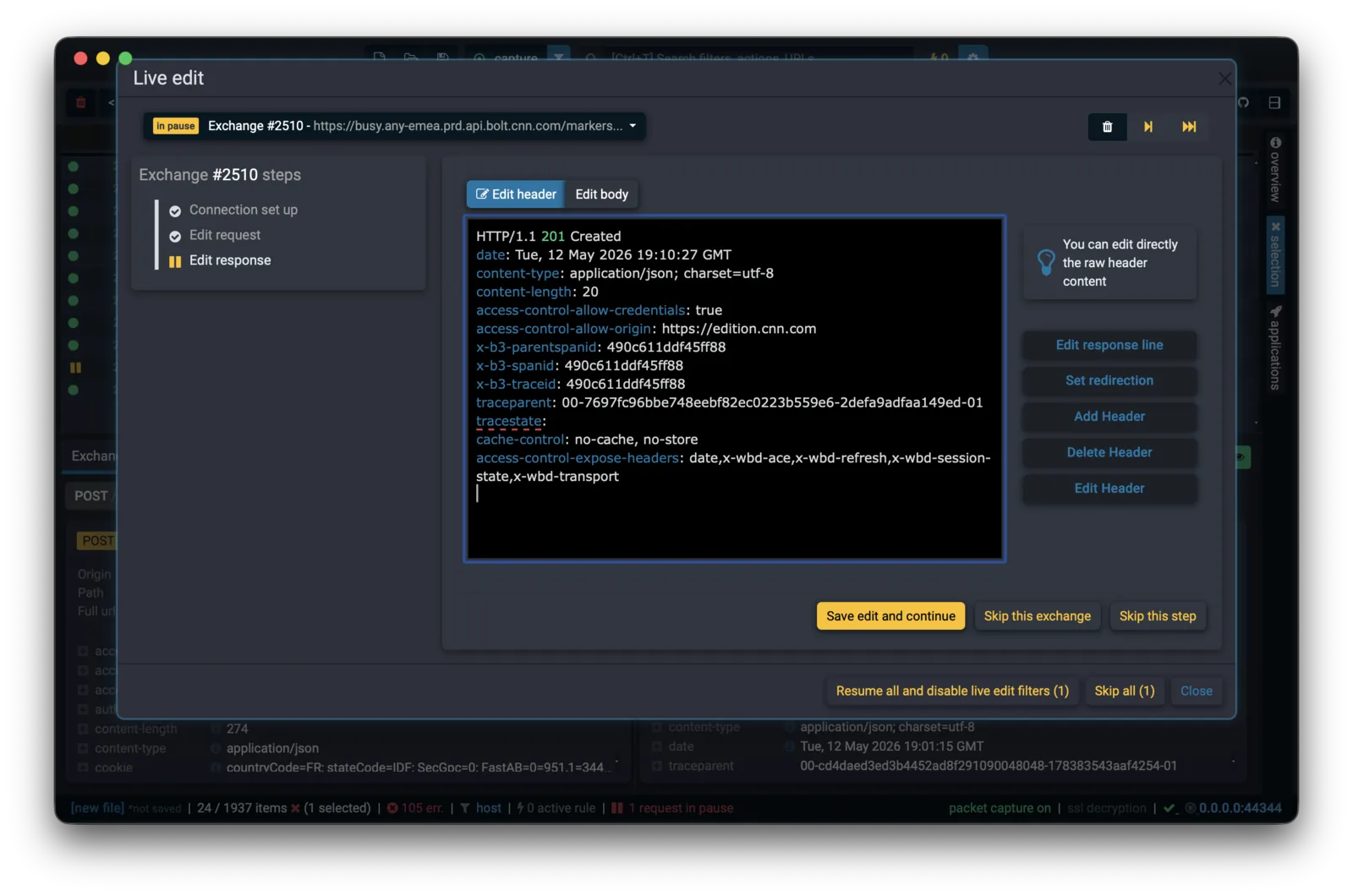
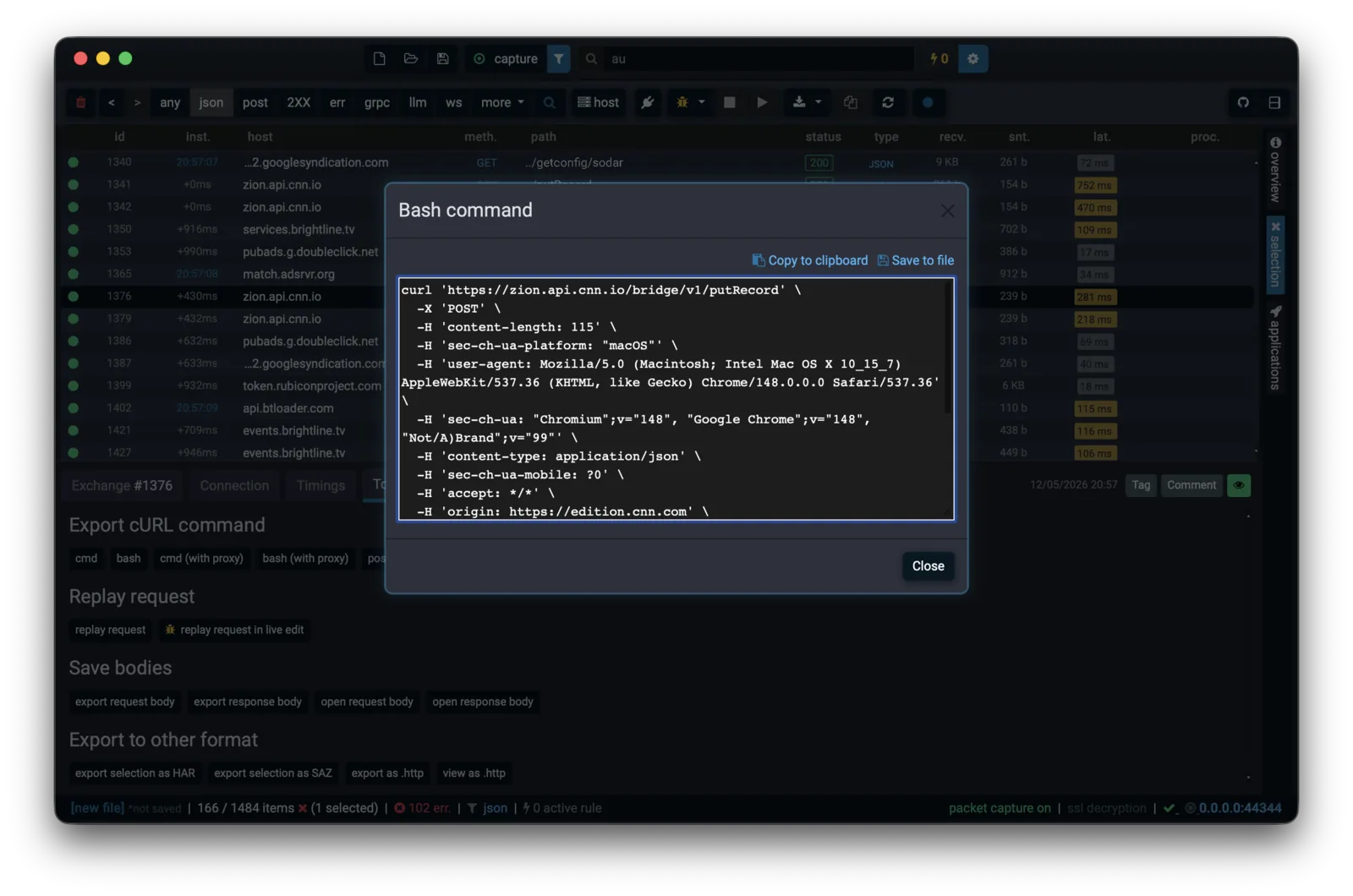
One click out: HAR for browser tooling, SAZ for Fiddler users, raw PCAPNG with embedded SSL keys for Wireshark, cURL commands (cmd, bash, with proxy) and .http scratch files for VS Code and JetBrains REST clients.
Free and unlimited. Fluxzy Desktop Community Edition. No card, no cloud.
Download FreeFluxzy Connect brings the same wire-level HTTP debugging to Android. Inspect any app's traffic from your phone, with the rules and decoders you already know from the desktop.
A complete HTTP toolkit out of the box. No paid tier, no plugin store, no telemetry.
Access all Fluxzy features — from request recording to advanced traffic alteration — in your own code with the open-source Fluxzy NuGet packages.
Download Fluxzy for free and start capturing, analyzing, and modifying HTTP traffic in minutes.
Download Now